Ensuring absolute data integrity and the uncompromising verification of official sources are of the highest priority here, in order to proactively protect the user’s digital assets from elaborate phishing infrastructures and man-in-the-middle attacks. Any interaction that implies downloading executable files must be subjected to a strict empirical examination of the Uniform Resource Locator and the cryptographic certificates, as compromised access vectors will inevitably lead to the total loss of the transferred crypto assets.
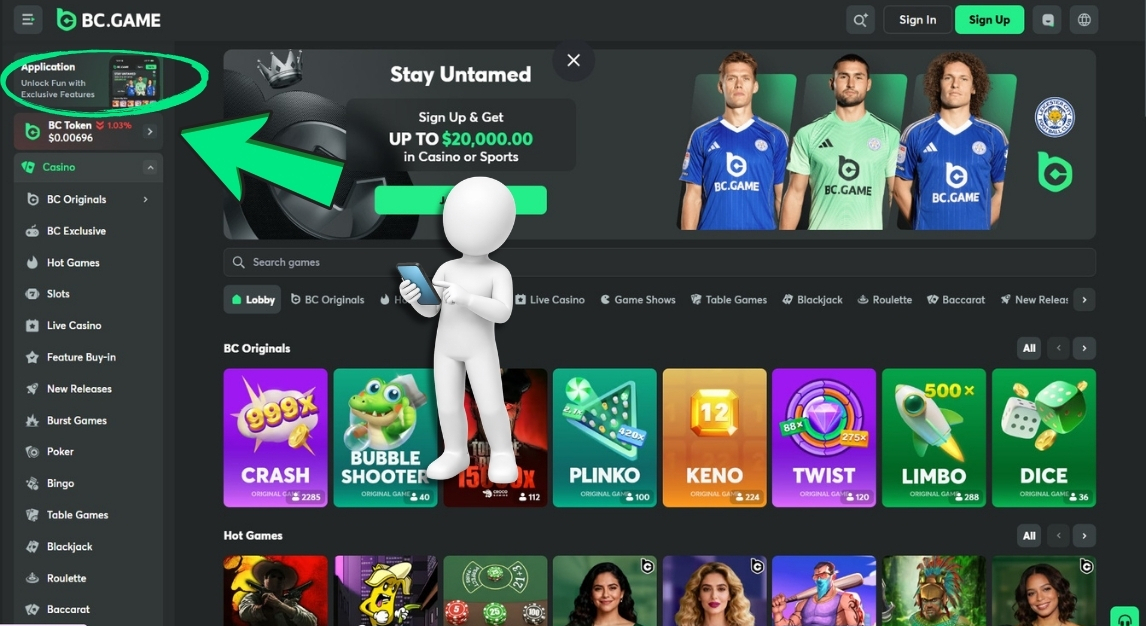
The Easiest Way: Using Bc.Game in the Mobile Browser
The technologically most universal and at the same most resource-efficient method for interacting with the complex infrastructure of bc games requires no installation of local binary files on the mobile device’s storage. The platform’s software developers utilize highly responsive web design, which dynamically adapts the Document Object Model, in real-time and based on CSS media queries, to the specific viewport metadata and physical resolution of the respective smartphone or tablet.

The procedural algorithm for this platform-independent access proceeds in the following strictly defined, sequential steps:
- Initialization of a current, standardized mobile web browser to ensure full compatibility with the employed JavaScript libraries.
- Manual entry of the exact, cryptographically verified domain bc.game into the address bar, strictly avoiding search engine results that could potentially point to manipulated mirror servers.
- Pressing the dedicated button for the login process after the DOM structure has fully loaded asynchronously and a secure TLS 1.3 connection has been established.
- Methodical navigation via the rendered hamburger menu or the static bottom navigation bar to the relevant core modules of the user interface, provided they are transmitted from the server to the client.
Once the cryptographic authentication of the session is successfully completed, the mobile user interface presents itself in its full functional and visual depth. Navigation to specific sections such as the personal, decentralized crypto wallet, the complex profile management, or the algorithm-based slot machines occurs seamlessly and without noticeable latency, provided a stable TCP/IP network connection exists. Even highly complex sub-areas, such as the mathematical matrices for bc.game esports betting or the dynamically updating odds for competitive bc game cs2 tournaments, are correctly interpreted, processed, and graphically displayed by the mobile browser’s rendering engine. A significant information-technological advantage of this purely browser-based approach lies in the absolute obsolescence of manual software updates, as all CSS stylesheets, JavaScript resources, and WebGL components are loaded into the local cache directly from the server in their most current, security-patched version with each new page view.
Bc Game Download iOS: Options Without the Store
The extraordinarily restrictive guidelines of the Apple App Store regarding the distribution of applications that integrate cryptographic transactions, smart contracts, and stochastic probability games usually prevent the provision of native, compiled binary files via this highly centralized and controlled infrastructure. Consequently, in empirical practice, there is typically no classic bc game download ios via the conventional distribution path of the iOS ecosystem, which makes the implementation of alternative, intelligent web-based application models by the platform engineers absolutely necessary. The primary technological solution for this restriction manifests in the advanced architecture of the Progressive Web App, which systematically blurs the classic boundaries between a regular website and a native application by utilizing specific Safari browser APIs to simulate an isolated, app-like full-screen environment on the end device.
The installation process of such a PWA requires the user’s conscious, manual interaction with the menu structure of the Safari browser. After accessing and verifying the official bc gaming website, the system’s native “Share” menu must be opened and the specific function “Add to Home Screen” selected. At this exact moment, the iOS operating system extracts the so-called Web App Manifest of the website, which defines the essential metadata, the absolute paths to the high-resolution icons, and the specific display properties, in order to generate a locally stored start icon on the home screen. From then on, this icon launches the application without visible address or navigation bars.

Should the platform hypothetically offer alternative installation profiles or external enterprise certificates for iOS for download on its user interface, extreme analytical caution is advised, as installing configuration profiles from unregulated sources can grant the provider extremely extensive system rights at the kernel level, which could potentially lead to the complete compromise of the entire end device. If the user interface offers no such options and only the described path via the browser or the PWA remains, this must be accepted as an objective architectural fact of the current software iteration. Actively searching for third-party links on forums or unregulated portals that suggest a direct bc game download must be categorically avoided, as these links will, with a probability bordering on certainty, point to phishing infrastructures programmed to drain crypto wallets by injecting malicious code.
Mobile Convenience Settings
After successfully establishing mobile access, regardless of whether it is via an isolated PWA environment or a regular tab in a mobile browser, the platform’s software architecture offers specific ergonomic parameters for optimizing Human-Computer Interaction. In the dedicated profile settings, usually accessible via the main menu of the user interface, various configurations can be made, provided these modules are unlocked in the specific mobile UI and rendered by the server. Localization settings allow precise switching of the linguistic language output, while configuring the fiat currency display enables the visual conversion of complex crypto holdings into understandable equivalents such as USD or EUR, drastically reducing cognitive load when evaluating wagering volumes.
If the mobile operating system and the browser used grant the corresponding permissions according to W3C standards, the parameters for push notifications can also be precisely adjusted to keep the user informed in real-time about incoming blockchain transaction confirmations or the algorithmic allocation of a bc game no deposit bonus. Such a bonus systemically manifests as exactly 1 daily spin on the ‘Lucky Spin’ wheel, whose random number generator is limited to a maximum mathematical payout limit of 5 BTC. Beyond the platform-specific interface settings, it falls within the information-technological responsibility of the user to proactively optimize the performance parameters of their own end device.
Regularly manually clearing the local browser cache prevents latency when executing memory-intensive WebGL animations or high-resolution live dealer streams. Ensuring an absolutely stable, high-frequency internet connection, ideally via 5G mobile standards or interference-free broadband Wi-Fi, is also mandatory to avoid asynchronous communication breakdowns when transmitting betting hashes to the bc.game server architecture, which in the event of disconnects could lead to procedural conflicts in the evaluation of smart contracts.
Staying Safe on the Go in the Bc.Game Casino
The inherent mobility of use on smartphones and tablets entails significantly altered and often much more critical attack vectors for potential security compromises of the digital identity. When interacting with the algorithms in the bc.game casino in public spaces, the strict and uncompromising adherence to cryptographic and operational hygiene is of existential importance for preserving digital assets. The fundamental axiom of applied information security here is that under all circumstances, only the officially verified main domain may be used to establish a connection. The statistical probability of encountering malicious mirror sites is drastically increased in mobile searches, as long URLs in the address bars of mobile browsers are often visually truncated, allowing subtle typographical manipulations to easily escape human perception.

Another highly critical aspect of network security is the data transmission architecture in unsecured public environments. Using unencrypted Wi-Fi hotspots at airports, train stations, or in restaurants opens up significant attack surfaces for so-called man-in-the-middle attacks, where malicious actors can intercept, read, and in the worst case, manipulate the unencrypted data traffic.
Implementing a Virtual Private Network on the mobile device encrypts the entire data tunnel with strong asymmetric algorithms and completely neutralizes this specific risk at the protocol level. Regarding session management, the absolute scientific maxim applies that after interaction ends, an active, manual logout must be performed via the user interface menu to invalidate the current session token on the server. This applies especially if the device could potentially also be used by third parties or if no strict biometric locking mechanisms are activated at the operating system level. The device-side function of most browsers to conveniently and automatically save access data and passwords must be strictly deactivated for interfaces that manage crypto assets, as in the event of physical loss or theft of the end device, immediate full access to the financial wallet would otherwise be inevitably compromised.
Support on the Smartphone: Finding Help

The architecture of modern communication interfaces integrates the customer service infrastructure directly into the mobile application layer to ensure immediate information exchange with operators in the event of algorithmic anomalies, display problems in the DOM, or procedural questions. Should irregularities occur during mobile use of the platform, whether in the validation of a complex, delayed blockchain transaction, the exact calculation of the 360% bonus accumulation on the fourth qualifying deposit, or the evaluation of specific rollover conditions, the support function must be accessed directly via the user interface to initiate clarification at the database level.
In the mobile display of the frontend, this essential service function is usually found in the form of a fixed, floating interaction symbol, often visualized as a minimalist chat icon and permanently positioned in the lower right or left corner of the viewport above other DOM elements. Alternatively, the communication module is embedded deep within the semantic structure of the main menu under standardized nomenclature such as “Help,” “Support,” or “Live Chat.” Initiating this module opens an asynchronous communication protocol based on advanced WebSocket technology, which establishes a bidirectional, text-based real-time connection to the support clusters.
For document-intensive processes, such as submitting cryptographically secured verification documents within the framework of mandatory Know-Your-Customer protocols or filing detailed error logs, the platform also provides an asynchronous email interface, which is ideally suited for the precise presentation of highly complex information-technological matters where asynchronous processing time is methodologically acceptable.