From an information theory perspective, an official login process requires entering sensitive cryptographic or alphanumeric data into a server environment secured by state-of-the-art TLS certificates, which guarantees the integrity of data packets during transmission over the public internet. The absolute security of the account, which in the architectural context of the platform effectively functions as a digital crypto wallet with extensive financial permissions, is only guaranteed if the basic parameters of network security are empirically validated before the first data packet is transmitted. Successfully establishing a secure and verified cryptographic session forms the indispensable foundation for any further algorithmic interaction, whether it be placing complex mathematical bets, managing digital assets, or claiming promotion-based incentives.
A 45-Second Security Start Before Logging In
Before initializing asynchronous data exchange with the server clusters, a precise security check, calibrated to about 45 seconds, must be carried out. This is to be regarded as an essential component of digital hygiene and statistically significantly minimizes the risk of account takeover by unauthorized third parties. The implementation of these preventive measures is based on the fundamental paradigms of applied cybersecurity and requires a systematic processing of specific checkpoints before any interaction with the graphical user interface takes place. Blind trust in search engine results or external links represents the single biggest risk factor when dealing with cryptographic platforms, which is why endpoint verification must always be done manually and based on objective indicators.

The following preventive steps must be carried out obligatorily:
- Verification of the Uniform Resource Locator (URL): The browser’s address bar must be checked for typographical anomalies, so-called typosquatting, whereby the domain must be exactly bc.game, entirely without appended prefixes, hyphens, or different top-level domains.
- Validation of the cryptographic certificate: Encryption via HTTPS must be verified; the padlock symbol in the browser must indicate a valid, non-expired certificate from a recognized Certificate Authority.
- Update the rendering engine: The web browser used must be updated to the latest version to ensure that no known JavaScript vulnerabilities or weaknesses in DOM processing can be exploited.
- Avoid external redirects: Authentication via floating banners, pop-ups on third-party sites, or unsolicited email links must be categorically avoided, as these mechanisms often redirect to compromised mirror servers or malicious infrastructures.
- Disable third-party scripts: Browser extensions with unverified source code should be temporarily disabled to prevent potential interception of keyboard inputs or the reading of session cookies by faulty or malicious add-ons.
Which Options May Be Available in the Bc Game Interface
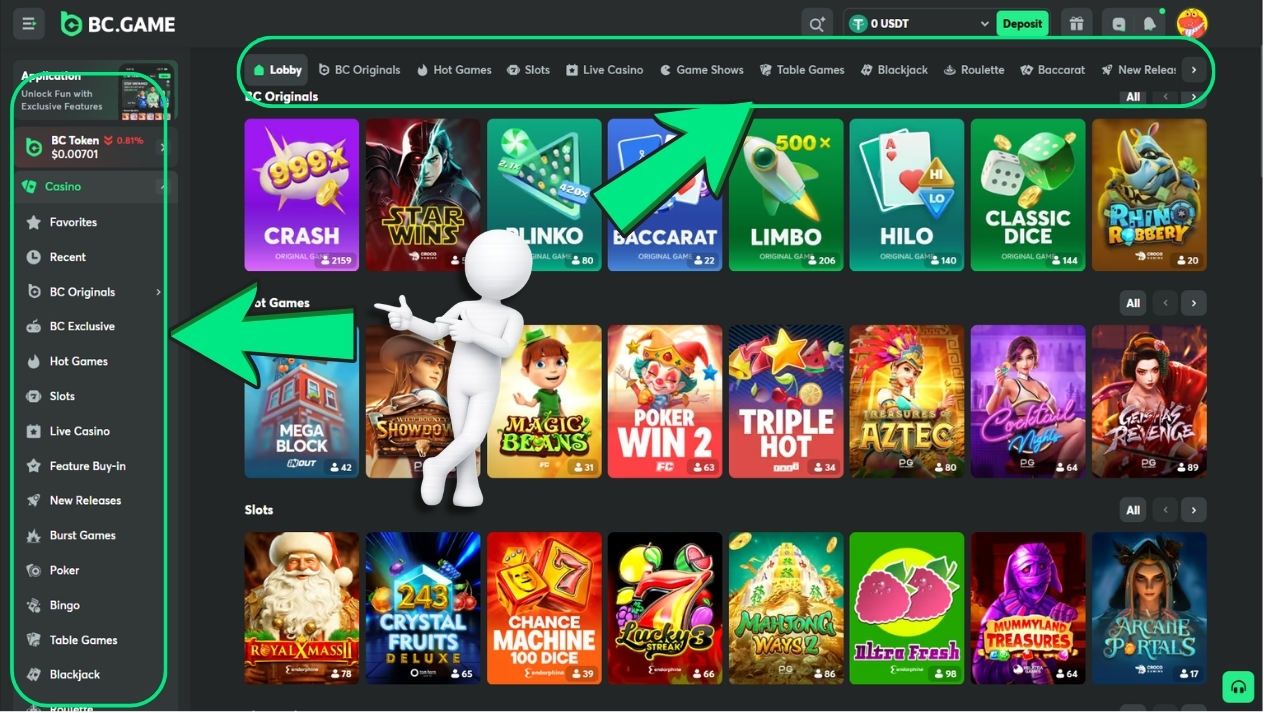
The frontend architecture of the platform is modular and dynamically designed, which means that users may be offered different vectors for identity verification depending on regional parameters, temporary A/B tests, or specific device recognition. The visual display of these options in the user interface is controlled by server-side scripts and does not require the installation of any local binary files, unless a legitimate bc game download for a mobile application is explicitly initiated. It is an essential characteristic of modern web applications that not all theoretically implemented authentication modules are necessarily rendered simultaneously on the graphical interface; instead, the interface adaptively adjusts to the most probable usage scenarios of the respective target audience.
The standard interface typically manifests specific input methods, representing different technological paradigms of authentication. The classic email login requires entering a valid SMTP address paired with an alphanumeric hash, while the wallet login delegates identity verification to a decentralized Web3 interface. Furthermore, in certain configurations, the system integrates OAuth interfaces for social logins, where an external authentication provider handles user data verification and only transmits a cryptographic token to the bc games infrastructure. An additional option for registration using a purely alphanumeric username is only usable if the input form explicitly renders this specific field and the underlying database architecture can process the corresponding primary keys.
Registration via Email at Bc.Game
The process of account creation using email is based on storing a singular, relational dataset in the platform’s backend infrastructure, requiring absolute precision during initial data entry to algorithmically preclude subsequent complications during verification or withdrawal processes. The processing of the entered strings is subject to strict validation rules, whereby the password is never stored in plain text, but exclusively as an asymmetrically encrypted, so-called salted hash in the databases, to protect user data even in the event of a hypothetical server compromise. The delivery of the necessary system emails to verify ownership of the mailbox depends on error-free server communication via the Simple Mail Transfer Protocol and the corresponding spam filters of the receiving providers.
The procedural sequence of registration proceeds in the following defined phases:
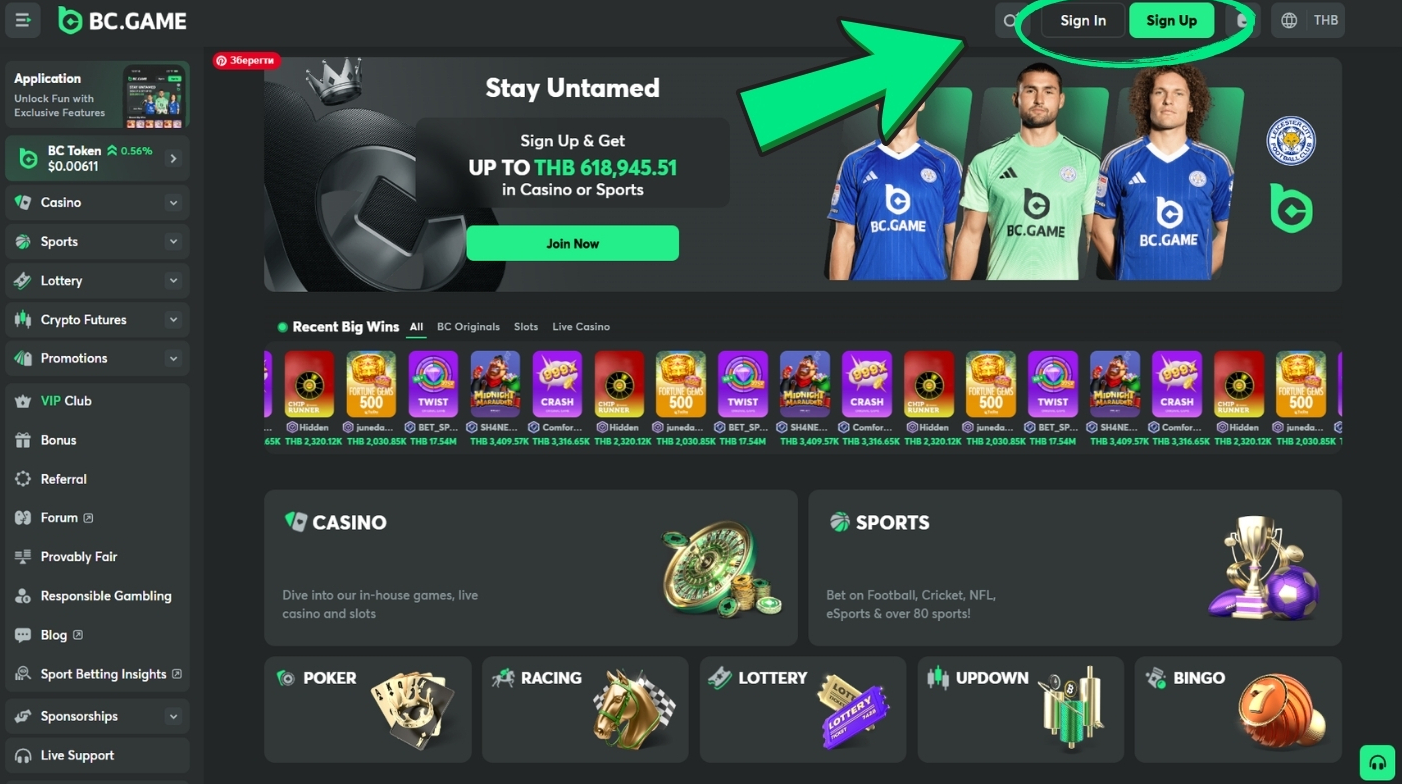
- Access the registration form: The dedicated module for account creation is accessed in the main navigation of the verified homepage.
- Enter basic data: The valid email address and an entropically strong password (consisting of upper and lower case letters, digits, and special characters) are entered into the designated input fields.
- Submit the data packet: By pressing the confirmation button, an API call is sent to the servers, whereupon the system initiates an asynchronous verification cycle.
- Enter the authentication token: A numerical code or cryptographic hyperlink sent to the specified email address must be verified within the interface within a defined time window.
- Troubleshooting delivery errors: If the confirmation email fails to arrive, systematically checking the local folders for “Spam” or “Promotions” is mandatory; only if the result is negative should the resend function be triggered via the user interface.

Wallet Login: Signature, Network, and Typical Errors
Web3 authentication represents the currently most advanced access method in the architecture of decentralized applications, as it eliminates any need for central storage of sensitive credentials on the servers of the operating company. Communication and identity verification occur directly and asynchronously between the local, browser-based or mobile decentralized wallet and the platform’s RPC interface. When selecting this method, the frontend sends a request to the wallet software, whereupon a specific cryptographic message must be signed using the Elliptic Curve Digital Signature Algorithm, serving as cryptographic proof of the legitimate ownership of the private key corresponding to the public blockchain address.

When initializing these so-called zero-gas signatures, specific communication anomalies can occur, the resolution of which requires a methodical approach.
- Network incompatibility: A common error vector is selecting an incompatible or testnet-based blockchain network within the wallet software, which immediately blocks the handshake by the API.
- Signature request timeout: In case of browser communication latency, the signature request may expire; in this case, the process must be manually canceled in the wallet and re-initiated via the platform’s UI.
- Outdated software architecture: A pending update to the wallet extension or the browser can hinder the execution of essential JavaScript commands, making regular updates indispensable.
- Blocking by restrictive add-ons: Strict ad blockers or tracking protection extensions may falsely classify the RPC calls between the website and the wallet as malicious scripts and prevent execution.
- Managing connections: If the platform UI provides corresponding configuration menus, existing wallet connections can be subsequently canceled or reconfigured in the personal profile.
Username Registration
Under certain configurations, the system architecture may provide the option of a freely selectable, alphanumeric identifier in the registration form, which is subject to strict database-technical restrictions to ensure the integrity of user assignment. The chosen string must absolutely fulfill the parameter of absolute uniqueness, as it functions in the backend as the primary reference key for all subsequent transactions, betting histories, and bonus allocations. The server-side validation logic usually limits the length of the username to precisely defined specifications, from a minimum of 3 to a maximum of 14 characters, and systematically excludes specific special characters or SQL command syntax to proactively neutralize injection vulnerabilities.
Initial Settings After Bc Game Login
After successful authentication and the generation of a valid session token, an immediate calibration of the account settings is essential to define the operational, visual, and security-related interaction levels for all subsequent activities on the platform. The personal profile acts as the central control point for all user preferences and system configurations, whereby adjustments here have a direct influence on the cognitive grasp of stakes and communication with the servers. A systematic review of the preset parameters prevents later confusion when evaluating odds or interpreting transaction histories.
The following parameters in the profile area should be configured as a priority after the initial login:
- Localization of the user interface: The language setting must be verified and adjusted if necessary to ensure that complex terms of service or betting rules can be understood linguistically without errors.
- Definition of the fiat currency display: Setting the preferred reference currency visually converts existing crypto balances, which significantly simplifies the assessment of betting volumes in resource-intensive sectors such as bc.game esports.
- Calibration of system notifications: If the interface displays corresponding controls, the parameters for email and push notifications should be adjusted to receive only relevant transaction confirmations or security-critical alerts.
- Monitoring of active sessions: The ‘Active Sessions’ module requires special analytical attention, as it logs all IP addresses, geographical locations, and end devices currently authorized with a valid token.
- Termination of unauthorized access: For reasons of uncompromising system security, any unknown, outdated, or geographically illogical sessions must be immediately terminated manually via the corresponding button in the interface.
Account Protection in the Sense of Bc Gaming: Practical Measures
The highly decentralized nature of asset management on cryptographic applications transfers the full responsibility for the security of digital values and personal data entirely to the end-user level. Account protection is therefore not based solely on the operating company’s firewalls, but requires the strict and consistent application of established cryptographic protocols as well as preventive operational behaviors when handling access data. Neglecting these measures often leads in practice to irreversible losses of crypto assets, as blockchain transactions, due to their mathematical nature, cannot be canceled or traced back once confirmed in the network.
As a fundamental measure of information security, an absolutely unique, highly complex password must be defined for access, ideally generated and managed by a locally encrypted or trustworthy cloud-based password manager to prevent credential stuffing attacks. The use of two-factor authentication via standardized Time-based One-Time Passwords, regenerated every thirty seconds by external applications such as Google Authenticator, must be implemented compulsorily, as it effectively neutralizes the attack surface in the event of potentially compromised basic access data. If the interface allows it, the anti-phishing code should be configured; this is a user-defined, alphanumeric string that the bc games servers will henceforth integrate into every legitimate outgoing email, whereby fraudulent communication attempts can be immediately unmasked by the absence of this code. On the operational hardware level, the strict maxim also applies that when using end devices not under one’s sole and exclusive control, a physical, active logout via the menu is absolutely necessary after completing a session, as merely closing the browser window usually does not immediately invalidate the session cookie.
Common Bc.Game Login Problems and Quick Solutions
Systematic evaluation of support metrics and server logs empirically demonstrates that the overwhelming majority of access anomalies and error messages during the authentication process are not due to structural server failures or database errors, but are primarily caused by asynchronous inputs, expired tokens, or client-side misconfigurations in the web browser. These software-based problems can usually be identified and resolved in the shortest possible time through methodical troubleshooting and understanding of the underlying web technologies. The server architecture is designed to restrictively block access for security reasons when deviant or faulty data packets are received.
An incorrect alphanumeric dataset, often caused by the unnoticed swapping of specific keys or an accidentally activated Caps Lock, represents by far the most common error vector. In the event of an actual loss of the cryptographic password hash, the implemented “Forgot password” function must be initiated, which generates a temporary, very time-limited recovery link. If this system-generated email fails to arrive, server-side greylisting by one’s own email provider is the most likely information-technological cause; waiting exactly 15 minutes before making another request via the interface is absolutely indicated in this scenario to avoid blocking the SMTP servers with spam requests.

If the web interface suddenly presents a CAPTCHA challenge, the network’s preventive DDoS protection mechanisms are engaging, requiring manual human interaction to solve complex visual tasks. Temporary blocks resulting from multiple failed authentication attempts are automatically lifted after a time window defined by the algorithm expires, while problems with invalid sessions require physically deleting local browser cookies and the cache. Potentially occurring regional access restrictions result from the geolocation analysis of the requesting IP address and are based on the strict licensing requirements of the respective regulatory authorities; in these cases, the architecture automatically blocks API access to the bc.game casino. If access is unexpectedly denied despite an existing bc game no deposit bonus, such as the daily free spin on the wheel, the validity of the underlying session tokens and network stability must be clarified as a priority before further steps are taken.